Health Care
Black Hat USA 2023 NOC: Community Assurance
The Black Hat Community Operations Middle (NOC) supplies a excessive safety, excessive availability community in one of the vital demanding environments on the earth – the Black Hat occasion.
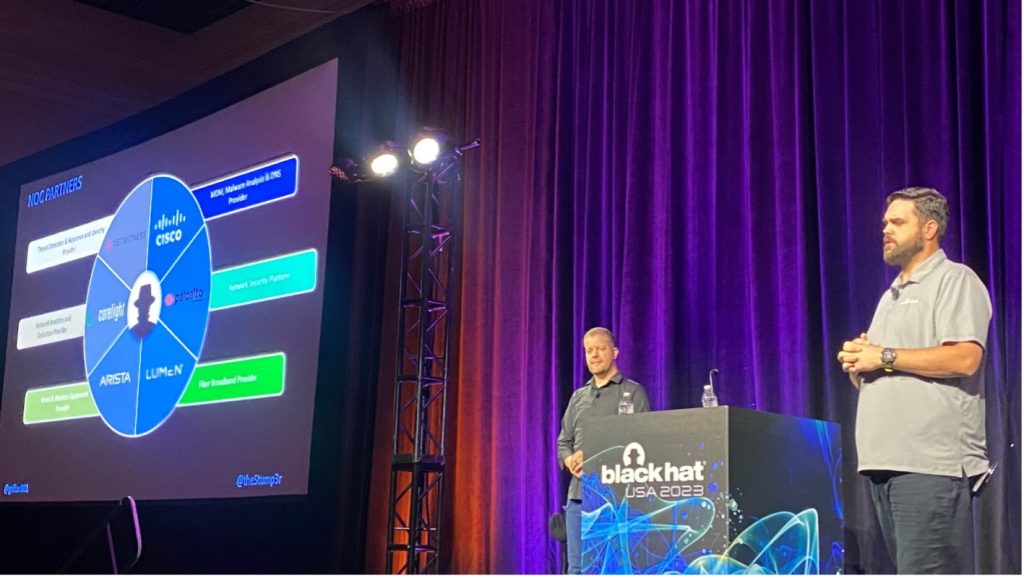
The NOC companions are chosen by Black Hat, with Arista, Cisco, Corelight, Lumen, NetWitness and Palo Alto Networks delivering from Las Vegas this 12 months. We admire Iain Thompson of The Register, for taking time to attend a NOC presentation and tour the operations. Take a look at Iain’s article: ‘Contained in the Black Hat community operations middle, volunteers work in geek heaven.’
We additionally present built-in safety, visibility and automation: a SOC (Safety Operations Middle) contained in the NOC, with Grifter and Bart because the leaders.
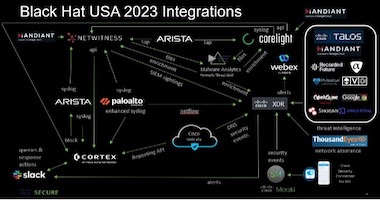
Integration is vital to success within the NOC. At every convention, we’ve a hack-a-thon: to create, show, take a look at, enhance and at last put into manufacturing new or improved integrations. To be a NOC associate, you should be keen to collaborate, share API (Automated Programming Interface) keys and documentation, and are available collectively (whilst market opponents) to safe the convention, for the nice of the attendees.

XDR (eXtended Detection and Response) Integrations
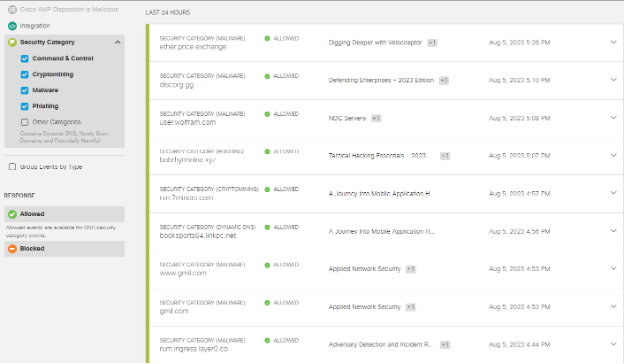
At Black Hat USA 2023, Cisco Safe was the official Cell Machine Administration, DNS (Area Title Service) and Malware Evaluation Supplier. We additionally deployed ThousandEyes for Community Assurance.
Because the wants of Black Hat developed, so have the Cisco Safe Applied sciences within the NOC:
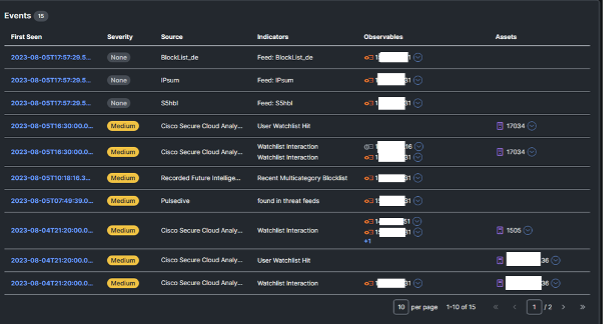
The Cisco XDR dashboard made it straightforward to see the standing of every of the related Cisco Safe applied sciences, and the standing of ThousandEyes brokers.
Under are the Cisco XDR integrations for Black Hat USA, empowering analysts to analyze Indicators of Compromise (IOC) in a short time, with one search. We admire alphaMountain.ai, Pulsedive and Recorded Future donating full licenses to the Black Hat USA 2023 NOC.

For instance, an IP tried AndroxGh0st Scanning Site visitors in opposition to the Registration server, blocked by Palo Alto Networks firewall.
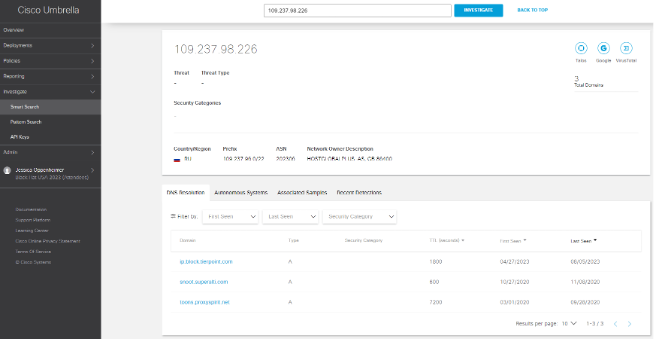
Investigation of the IP confirmed it was recognized malicious.
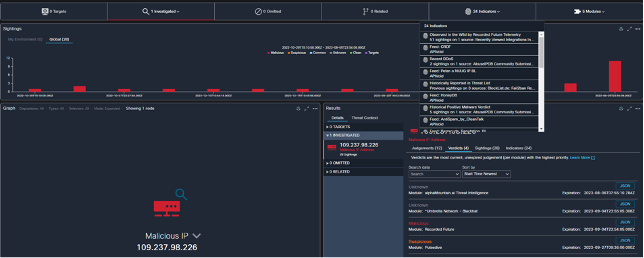
Additionally, the geo location in RU and recognized affiliated domains. With this info, the NOC management permitted the shunning of the IP.
File Evaluation and Teamwork within the NOC
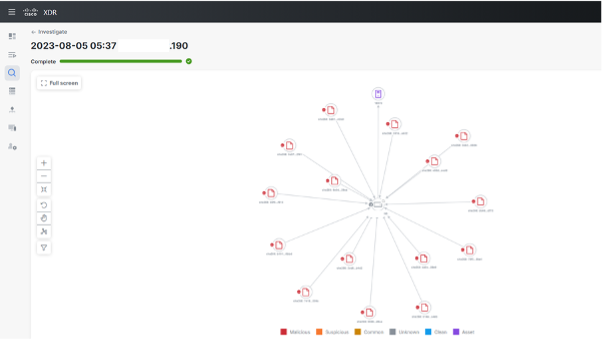
Corelight and NetWitness extracted practically 29,000 recordsdata from the convention community stream, which have been despatched for evaluation in Cisco Safe Malware Analytics (Risk Grid).

It was humorous to see the variety of Home windows replace recordsdata that have been downloaded at this premier cybersecurity convention. When file was convicted as malicious, we’d examine the context:
- Is it from a classroom, the place the subject is expounded to the conduct of the malware?
- Or, is from a briefing or a demo within the Enterprise Corridor?
- Is it propagating or confined to that single space?
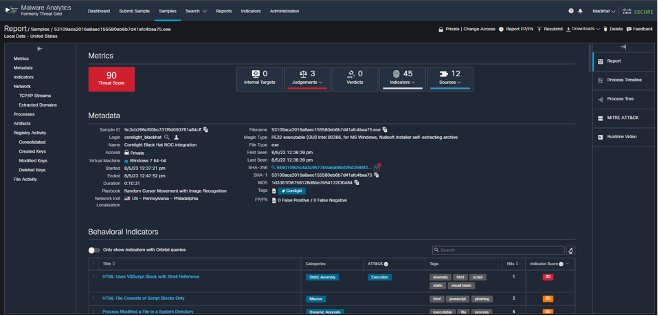
The pattern above was submitted by Corelight and investigation confirmed a number of downloads within the coaching class Home windows Reverse Engineering (+Rust) from Scratch (Zero Kernel & All Issues In-between), a certified exercise.

The ABCs of XDR within the NOC, by Ben Greenbaum
One of many many Cisco instruments in our Black Hat package was the newly introduced Cisco XDR. The highly effective, multi-faceted and dare I say it “prolonged” detection and response engine allowed us to simply meet the next targets:

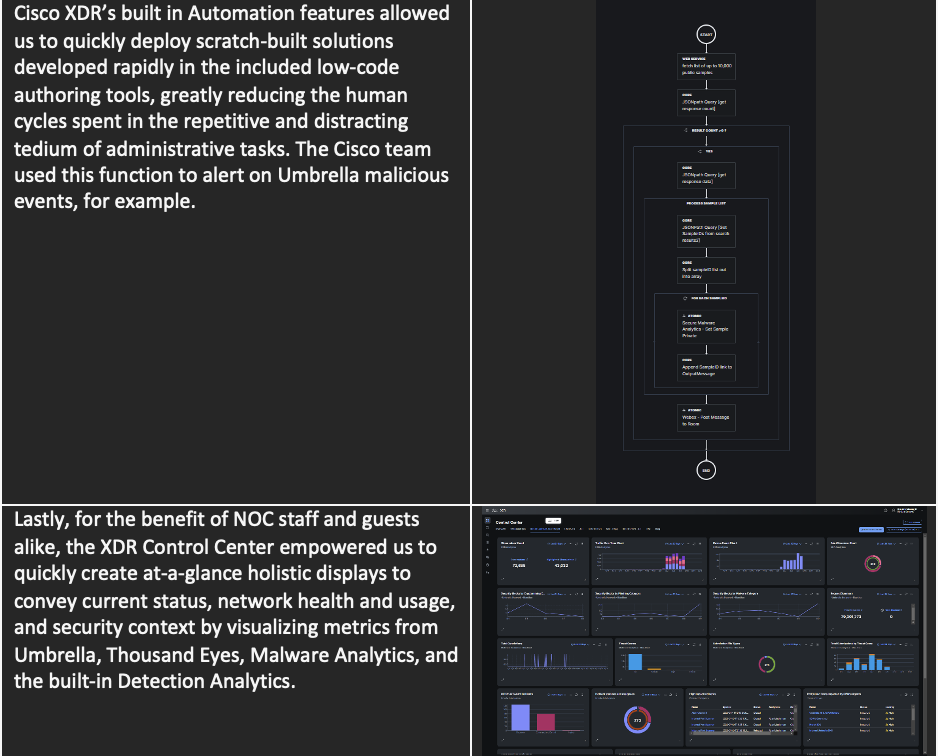
One of many much less public-facing advantages of this distinctive ecosystem is the flexibility for our engineers and product leaders to get face time with our friends at associate group, together with people who would usually – and rightfully – be thought of our opponents. As at Black Hat occasions previously, I obtained to take part in significant conversations concerning the intersection of utilization of Cisco and threerd social gathering merchandise, tweak our API plans and clearly specific the wants we’ve from our associate applied sciences to higher serve our prospects in widespread. This collaborative, cooperative challenge permits all our groups to enhance the way in which our merchandise work, and the way in which they work collectively, for the betterment of our prospects’ talents to satisfy their safety targets. Actually a novel scenario and one by which we’re grateful to take part.
Safe Cloud Analytics in XDR, by Adi Sankar
Safe Cloud Analytics (SCA) means that you can acquire the visibility and steady risk detection wanted to safe your public cloud, personal community and hybrid atmosphere. SCA can detect early indicators of compromise within the cloud or on-premises, together with insider risk exercise and malware, in addition to coverage violations, misconfigured cloud property, and consumer misuse. These NDR (Community Detection and Response) capabilities have now change into native performance inside Cisco XDR. Cisco XDR was out there beginning July 31st 2023, so it was a good time to place it by way of its paces on the Black Hat USA convention in August.
Cisco Telemetry Dealer Deployment
Cisco Telemetry Dealer (CTB) routes and replicates telemetry information from a supply location(s) to a vacation spot shopper(s). CTB transforms information protocols from the exporter to the patron’s protocol of alternative and due to its flexibility CTB was chosen to pump information from the Black Hat community to SCA.
Usually, a CTB deployment requires a dealer node and a supervisor node. To cut back our on-prem foot print I proactively deployed a CTB supervisor node in AWS (Amazon Net Providers) (though this deployment just isn’t out there for purchasers but, cloud managed CTB is on the roadmap). Because the supervisor node was deployed already, we solely needed to deploy a dealer node on premise in ESXi.
With the 10G succesful dealer node deployed it was time to put in a particular plugin from engineering. This bundle just isn’t out there for purchasers and continues to be in beta, however we’re fortunate sufficient to have engineering help to check out the newest and biggest know-how Cisco has to supply (Particular shoutout to Junsong Zhao from engineering for his help). The plugin installs a move sensor inside a docker container. This enables CTB to ingest a SPAN from an Arista swap and rework it to IPFIX information. The move sensor plugin (previously Stealthwatch move sensor) makes use of a mixture of deep packet inspection and behavioral evaluation to determine anomalies and protocols in use throughout the community.
Along with the SPAN, we requested that Palo Alto ship NetFlow from their Firewalls to CTB. This enables us to seize telemetry from the sting units’ egress interface giving us insights into site visitors from the exterior web, inbound to the Blackhat community. Within the CTB supervisor node I configured each inputs to be exported to our SCA tenant.


 Non-public Community monitoring within the cloud
Non-public Community monitoring within the cloud
First, we have to configure SCA by turning on all of the NetFlow primarily based alerts. On this case it was already performed since we used the identical tenant for a Blackhat Singapore. Nevertheless, this motion could be automated utilizing the API api/v3/alerts/publish_preferences/ by setting each “should_publish” and “auto_post_to_securex” to true within the payload. Subsequent, we have to configure entity teams in SCA to correspond with inner Blackhat community. Since subnets can change convention to convention, I automated this configuration utilizing a workflow in XDR Automate.

The subnets are documented in a CSV file from which the workflow parses 3 fields: the CIDR of the subnet, a reputation and an outline. Utilizing these fields to execute a POST name to the SCA /v3/entitygroups/entitygroups/ API creates the corresponding entity teams. A lot quicker than manually configuring 111 entity teams!

Now that we’ve community telemetry information flowing to the cloud SCA can create detections in XDR. SCA begins with observations which flip into alerts that are then correlated into assault chains earlier than lastly creating an Incident. As soon as the incident is created it’s submitted for precedence scoring and enrichment. Enrichment queries the opposite built-in applied sciences resembling Umbrella, Netwitness and risk intelligence sources concerning the IOC’s from the incident, bringing in further context.

SCA detected 289 alerts together with Suspected Port Abuse, Inside Port Scanner, New Uncommon DNS Resolver,and Protocol Violation (Geographic). SCA correlated 9 assault chains together with one assault chain with a complete of 103 alerts and 91 hosts on the community. These assault chains have been seen as incidents throughout the XDR console and investigated by risk hunters within the NOC.

Conclusion
Cisco XDR collects telemetry from a number of safety controls, conducts analytics on that telemetry to reach at a detection of maliciousness, and permits for an environment friendly and efficient response to these detections. We used Cisco XDR to its fullest within the NOC from automation workflows, to analyzing community telemetry, to aggregating risk intelligence, investigating incidents, preserving monitor of managed units and rather more!
Hunter summer time camp is again. Talos IR risk searching throughout Black Hat USA 2023, by Jerzy ‘Yuri’ Kramarz
That is the second 12 months Talos Incident Response is supporting Community Operations Centre (NOC) through the Black Hat USA convention, in a risk searching capability.

My goal was to make use of multi-vendor know-how stacks to detect and cease ongoing assaults on key infrastructure externally and internally and determine potential compromises to attendees’ programs. To perform this, the risk searching group targeted on answering three key hypothesis-driven questions and matched that with information modeling throughout totally different know-how implementations deployed within the Black Hat NOC:
- Are there any attendees making an attempt to breach one another’s programs in or outdoors of a classroom atmosphere?
- Are there any attendees making an attempt to subvert any NOC Techniques?
- Are there any attendees compromised, and will we warn them?
Like final 12 months, evaluation began with understanding how the community structure is laid out, and what sort of information entry is granted to NOC from numerous companions contributing to the occasion. That is one thing that modifications yearly.
Nice many thanks go to our buddies from NetWitness, Corelight, Palo Alto Networks, Arista and Mandiant and plenty of others, for sharing full entry to their applied sciences to make sure that searching wasn’t contained to simply Cisco tools and that contextual intelligence might be gathered throughout totally different safety merchandise. Along with know-how entry, I additionally acquired nice assist and collaboration from associate groups concerned in Black Hat. In a number of circumstances, a number of groups have been contributing technical experience to determine and confirm potential indicators of compromise.
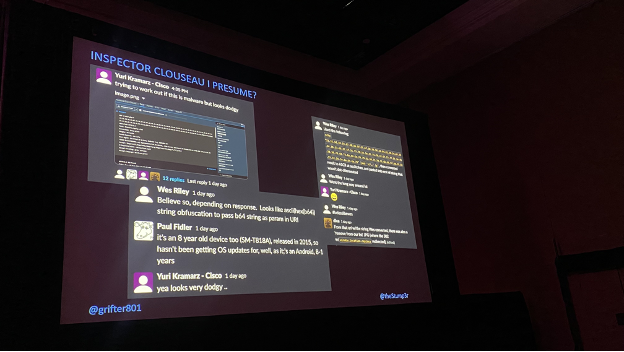
For our personal know-how stack, Cisco provided entry to Cisco XDR, Meraki, Cisco Safe Malware Analytics, Hundreds Eyes, Umbrella and Safe Cloud Analytics (previously often known as StealthWatch).
The Hunt
Our each day risk hunt began with gathering information and searching on the connections, packets and numerous telemetry gathered throughout the whole community safety stack in Cisco applied sciences and different platforms, resembling Palo Alto Networks or NetWitness XDR. Given the infrastructure was an agglomeration of varied applied sciences, it was crucial to develop a risk searching course of which supported every of the distributors. By combining entry to shut to 10 totally different applied sciences, our group gained a larger visibility into site visitors, however we additionally recognized just a few attention-grabbing situations of various units compromised on the Black Hat community.
One such instance was an AsyncRat-compromised system discovered with NetWitness XDR, primarily based on a selected key phrase situated within the SSL certificates. As seen within the screenshot beneath, the instrument permits for highly effective deep-packet-inspection evaluation.
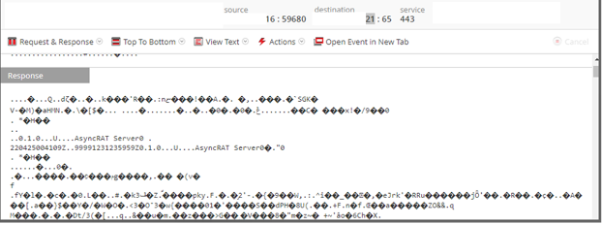
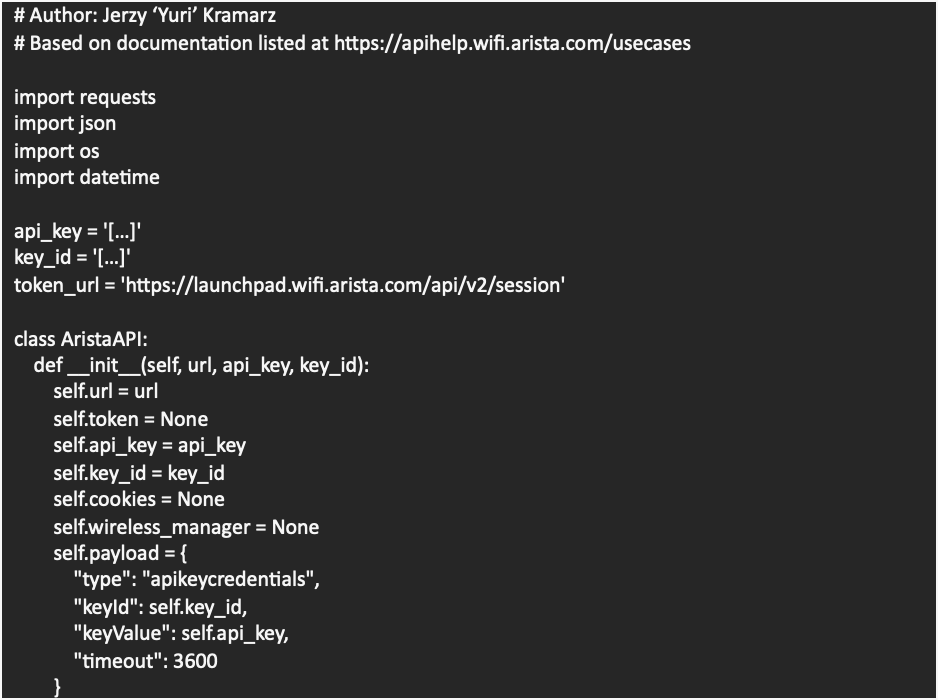
After constructive identification of the AsyncRat exercise, we used the Arista wi-fi API to trace the consumer to a selected coaching room and notified them about the truth that their machine seemed to be compromised. Generally some of these actions could be a part of a Black Hat coaching courses, however on this case, it appeared evident that the consumer was unaware of the official compromise. This little snippet of code helped us discover out the place attendees have been within the lecture rooms, primarily based on Wi-fi AP connection, so we might notify them about their compromised programs.


All through our evaluation we additionally recognized one other occasion of direct malware compromise and associated community communication which matched the exercise of an AutoIT.F trojan speaking over a command and management (C2) to a well-know malicious IP [link to a JoeBox report]. The C2 the adversary used was checking on TCP ports 2842 and 9999. The instance of AutoIT.F trojan request, noticed on the community could be discovered beneath.
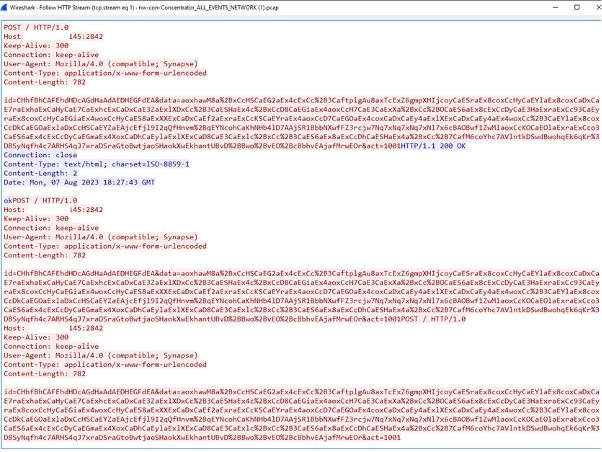
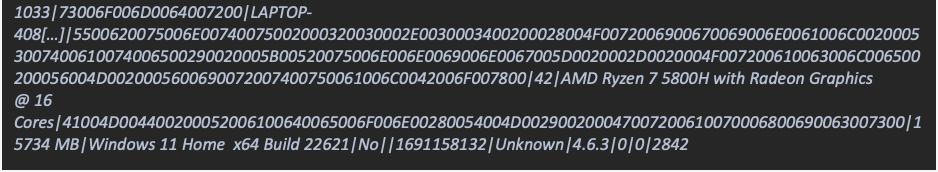
Above site visitors pattern was decoded, to extract C2 site visitors report and the next decoded strings seemed to be the ultimate payload. Discover that the payload included {hardware} specification, construct particulars and system title together with different particulars.
Likewise, on this case, we managed to trace the compromised system by way of the Wi-Fi connection and notifiy the consumer that their system seemed to be compromised.
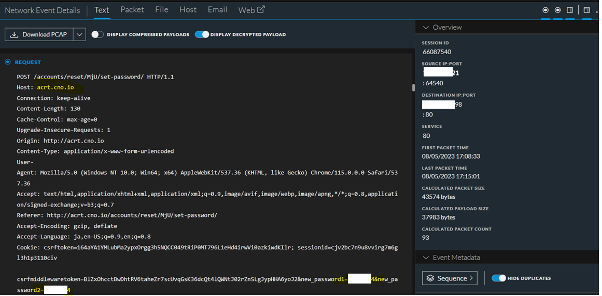
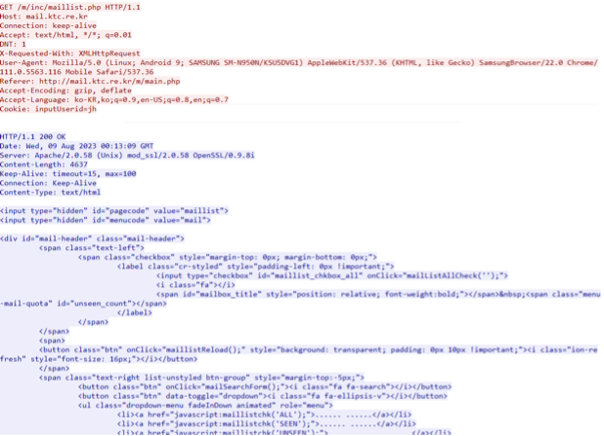
Clear Textual content authentication nonetheless exists in 2023
Though indirectly associated to malware an infection, we did uncover just a few different attention-grabbing findings throughout our risk hunt, together with quite a few examples of clear textual content site visitors disclosing e-mail credentials or authentication session cookies for number of purposes. In some situations, it was potential to look at clear-text LDAP bind makes an attempt which disclosed which group the machine belonged to or direct publicity of the username and password mixture by way of protocols resembling POP3, LDAP, HTTP (Hyper Textual content Switch Protocol) or FTP. All these protocols could be simply subverted by man-in-the-middle (MitM) assaults, permitting an adversary to authenticate in opposition to providers resembling e-mail. Under is an instance of the plain textual content authentication credentials and different particulars noticed by way of numerous platforms out there at Black Hat.
Different examples of clear textual content disclosure have been noticed by way of primary authentication which merely used base64 to encode the credentials transmitted over clear textual content. An instance of this was seen with an City VPN (Digital Non-public Community) supplier which seems to seize configuration recordsdata in clear textual content with primary authentication.

Just a few different situations of varied clear textual content protocols resembling IMAP have been additionally recognized on the community, which we have been stunned to nonetheless be use in 2023.

What was attention-grabbing to see is that a number of trendy cell purposes, resembling iPhone Mail, are glad to just accept poorly configured e-mail servers and use insecure providers to serve primary functionalities, resembling e-mail studying and writing. This resulted in quite a few emails being current on the community, as seen beneath:

This 12 months, we additionally recognized a number of cell purposes that not solely supported insecure protocols resembling IMAP, but in addition carried out direct communication in clear textual content, speaking every thing in clear textual content, together with consumer footage, as famous beneath:
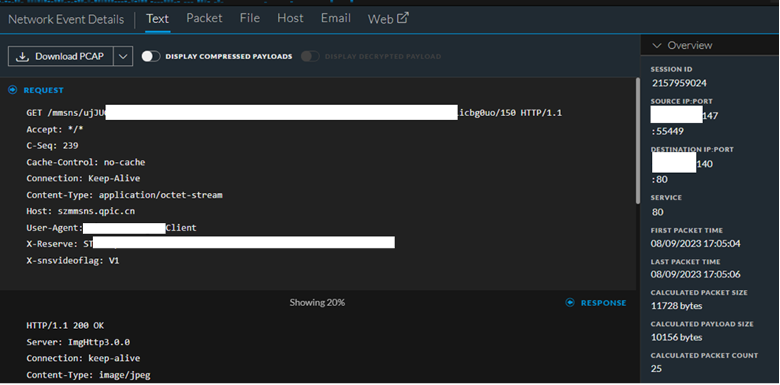
In a number of situations, the cell software additionally transmitted an authentication token in clear textual content:

Much more attention-grabbing was the truth that we’ve recognized just a few distributors making an attempt to obtain hyperlinks to patches over HTTP, as properly. In some situations, we’ve seen unique requests despatched over HTTP protocol with the “Location” header response in clear textual content pointing to an HTTPS location. Though I’d anticipate these patches to be signed, speaking over HTTP makes it fairly straightforward to switch the site visitors in MitM state of affairs to redirect downloads to separate areas.


There have been quite a few different examples of HTTP protocol used to carry out operations resembling studying emails by way of webmail portals or downloading PAC recordsdata which disclose inner community particulars as famous on the screenshots beneath.

Cisco XDR know-how in motion
Along with the standard know-how portfolio provided by Cisco and its companions, this 12 months was additionally the primary 12 months I had the pleasure of working with Cisco XDR console, which is a brand new Cisco product. The concept behind XDR is to provide a single “pane of glass” overview of all of the totally different alerts and applied sciences that work collectively to safe the atmosphere. A few of Cisco’s safety merchandise resembling Cisco Safe Endpoint for iOS and Umbrella have been related to by way of XDR platform and shared their alerts, so we might use these to realize a fast understanding of every thing that’s occurring on community from totally different applied sciences. From the risk searching perspective, this enables us to rapidly see the state of the community and what different units and applied sciences may be compromised or execute suspicious actions.
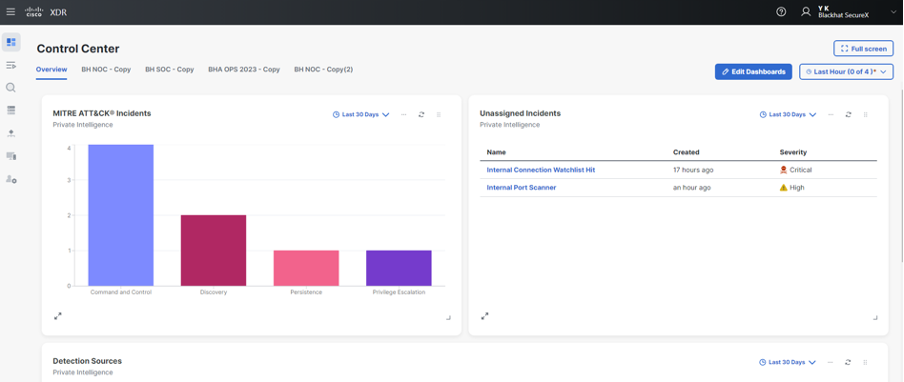

Whereas inner site visitors, we additionally discovered and plotted fairly just a few totally different port scans working throughout the inner and exterior community. Whereas we’d not cease these until they have been sustained and egregious, it was attention-grabbing to see totally different makes an attempt by college students to search out ports and units throughout networks. Good factor that community isolation was in place to forestall that.
The instance beneath exhibits fast exterior investigation utilizing XDR, which resulted in profitable identification of this sort of exercise. What triggered the alert was a collection of occasions which recognized scanning and the truth that suspected IP additionally had relationships with a number of malicious recordsdata seen in VirusTotal:

Based mostly on this evaluation, we rapidly confirmed that port scanning is certainly legitimate and decided which units have been impacted, as seen beneath. This, mixed with visibility from different instruments resembling Palo Alto Networks boundary firewalls, gave us stronger confidence in our raised alerts. The additional contextual info associated to malicious recordsdata additionally allowed us to substantiate that we’re coping with a suspicious IP.
All through the Black Hat convention, we noticed many alternative assaults spanning throughout totally different endpoints. It was useful to have the ability to filter on these assaults rapidly to search out the place the assault originated and whether or not it was a real constructive.

Utilizing the above view, it was additionally potential to straight observe what contributed to the calculation of malicious rating and what sources of risk intelligence might be used to determine how was the malicious rating calculated for every of the elements that made up the general alert.
It’s not nearly inner networks
By way of the exterior assaults, Log4J, SQL injections, OGLN exploitation makes an attempt, and all types of enumeration have been a each day incidence on the infrastructure and the purposes used for attendee registration, together with different typical web-based assaults resembling path traversals. The next desk summarizes a few of the noticed a few of the efficiently blocked assaults the place we’ve seen the largest quantity. Once more, our because of Palo Alto Networks for giving us entry to their Panorama platform, so we are able to observe numerous assaults in opposition to the Black Hat infrastructure.

General, we noticed a sizeable variety of port scans, floods, probes and all types of internet software exploitation makes an attempt displaying up each day at numerous peak hours. Happily, all of them have been efficiently recognized for context (is that this a part of a coaching class or demonstration?) and contained (if acceptable) earlier than inflicting any hurt to exterior programs. We even had a suspected Cobalt Strike server (179.43.189[.]250) [link to VirusTotal report] scanning our infrastructure and on the lookout for particular ports resembling 2013, 2017, 2015 and 2022. Given the truth that we might intercept boundary site visitors and examine particular PCAP (packet seize) dumps, we used all these assaults to determine numerous C2 servers for which we additionally hunted internally, to make sure that no inner system is compromised.

Community Assurance, by Ryan MacLennan and Adam Kilgore
Black Hat USA 2023 is the primary time we deployed a brand new community efficiency monitoring answer named ThousandEyes. There was a proof of idea of ThousandEyes capabilities at Black Hat Asia 2023, investigating a report of sluggish community entry. The investigation recognized the problem was not with the community, however with the latency in connecting to a server in Eire from Singapore. We have been requested to proactively convey this community visibility and assurance to Las Vegas.
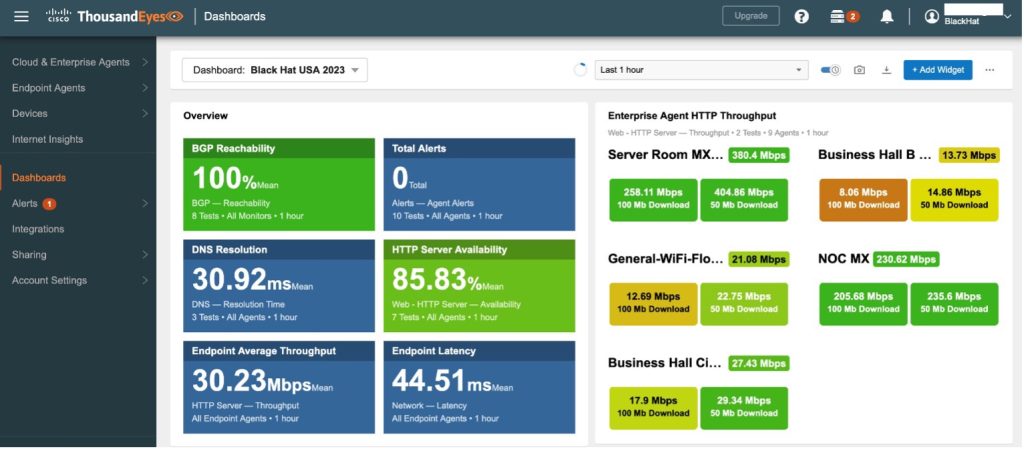
ThousandEyes makes use of each stationary Enterprise Brokers and cell Endpoint Brokers to measure community efficiency standards like availability, throughput, and latency. The picture beneath exhibits a few of the metrics captured by ThousandEyes, together with common latency info within the high half of the picture, and Layer 3 hops within the backside half of the picture with latency tracked for every community leg between the Layer 3 hops.
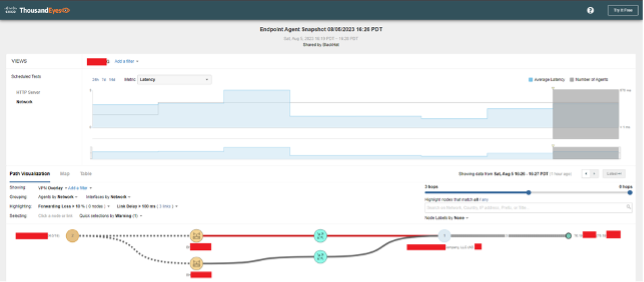
The ThousandEyes internet GUI can present information for one or many TE brokers. The screenshot beneath exhibits a number of brokers and their respective paths from their deployment factors to the Black Hat.com web site.

We additionally created a set of customized ThousandEyes dashboards for the Black Hat conference that tracked mixture metrics for the entire deployed brokers.
ThousandEyes Deployment
Ten ThousandEyes Enterprise Brokers have been deployed for the convention. These brokers have been moved all through totally different convention areas to observe community efficiency for essential occasions and providers. Endpoint Brokers have been additionally deployed on laptops of NOC technical affiliate personnel and used for cell diagnostic info in numerous investigations.
Coming into Black Hat with information of how the convention will likely be arrange was key in figuring out how we’d deploy ThousandEyes. Earlier than we arrived on the convention, we made a preliminary plan on how we’d deploy brokers across the convention. This included what sort of machine would run the agent, the connection sort, and tough areas of the place they’d be arrange. Within the picture beneath you may see we deliberate to deploy ThousandEyes brokers on Raspberry Pi’s and a Meraki MX equipment

The plan was to run all of the brokers on the wi-fi community. As soon as we arrived on the convention, we began prepping the Pi’s for the ThousandEyes picture that was supplied within the UI (Person Interface). The beneath picture exhibits us getting the Pi’s out of their packaging and setting them up for the imaging course of. This included putting in heatsinks and a fan.

After all of the Pi’s have been prepped, we began flashing the ThousandEyes (TE) picture onto every SD-Card. After flashing the SD-Playing cards, we wanted besides them up, get them related to the dashboard after which work on enabling the wi-fi. Whereas we had a enterprise case that known as for wi-fi TE brokers on Raspberry Pi, we did must clear a hurdle or wi-fi not being formally supported for the Pi TE agent. We needed to undergo a strategy of unlocking (jailbreaking) the brokers, putting in a number of networking libraries to allow the wi-fi interface, after which create boot up scripts to begin the wi-fi interface, get it related, and alter the routing to default to the wi-fi interface. You could find the code and information at this GitHub repository.
We confirmed that the wi-fi configurations have been working correctly and that they’d persist throughout boots. We began deploying the brokers across the convention as we deliberate and waited for all of them to come back up on our dashboard. Then we have been prepared to begin monitoring the convention and supply Community Assurance to Black Hat. No less than that’s what we thought. About half-hour after every Pi got here up in our dashboard, it will mysteriously go offline. Now we had some points we wanted to troubleshoot.
Troubleshooting the ThousandEyes Raspberry Pi Deployment
Now that our Pi’s had gone offline, we wanted to determine what was occurring. We took some again with us and allow them to run in a single day with one utilizing a wired connection and one on a wi-fi connection. The wi-fi one didn’t keep up all night time, whereas the wired one did. We seen that the wi-fi machine was considerably hotter than the wired one and this led us to the conclusion that the wi-fi interface was inflicting the Pi’s to overheat.
This conundrum had us confused as a result of we’ve our personal Pi’s, with no heatsinks or followers, utilizing wi-fi at house and so they by no means overheat. One thought we had was that the heatsinks weren’t cooling adequately as a result of the Pi kits we had used a thermal sticker as a substitute of thermal paste and clamp like a typical pc. The opposite was that the fan was not pushing sufficient air out of the case to maintain the inner temperature low. We reconfigured the fan to make use of extra voltage and flipped the fan from pulling air out of the case to pushing air in and onto the elements. Whereas a fan positioned straight on a CPU ought to pull the new air off the CPU, orienting the Raspberry Pi case fan to blow cooler air straight onto the CPU may end up in decrease temperatures. After re-orienting the fan, to blow onto the CPU, we didn’t have any new heating failures.
Working a few Pi’s with the brand new fan configuration all through the day proved to be the answer we wanted. With our mounted Pi’s now staying cooler, we have been in a position to full a secure deployment of ThousandEyes brokers across the convention.
ThousandEyes Use Case
Connectivity issues with the coaching rooms have been reported through the early days of the convention. We utilized a number of totally different strategies to gather diagnostic information straight from the reported downside areas. Whereas we had ThousandEyes brokers deployed all through the convention middle, downside stories from particular person rooms typically required a direct strategy that introduced a TE agent on to the issue space, typically concentrating on a selected wi-fi AP (Entry Factors) to gather diagnostic information from.
One particular use case concerned a report from the Jasmine G coaching room. A TE engineer traveled to Jasmine G and used a TE Endpoint Agent on a laptop computer to hook up with the Wi-Fi utilizing the PSK assigned to the coaching room. The TE engineer talked to the coach, who shared a selected internet useful resource that their coaching session relied on. The TE engineer created a selected take a look at for the room utilizing the net useful resource and picked up diagnostic information which confirmed excessive latency.
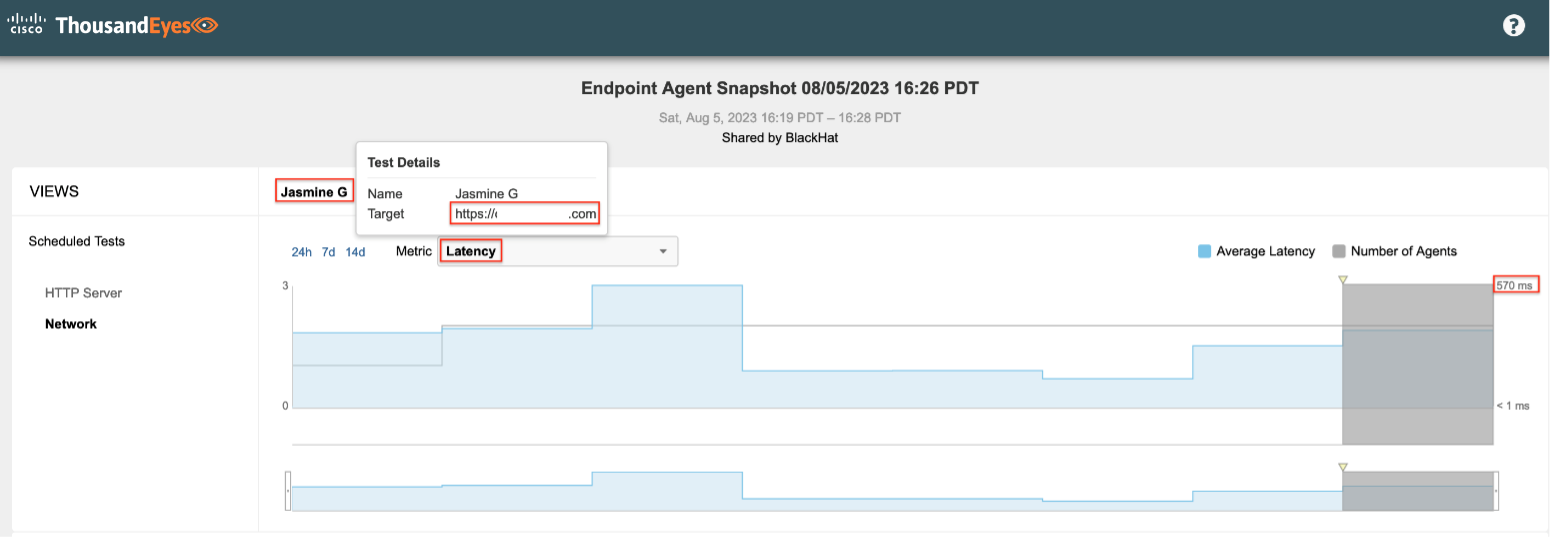
In the course of the assortment of the info, the TE agent related to 2 totally different wi-fi entry factors close to the coaching room and picked up latency information for each paths. The connection by way of one of many APs confirmed considerably greater latency than the opposite AP, as indicated by the crimson strains within the picture beneath.

ThousandEyes can generate searchable stories primarily based on take a look at information, resembling the info proven within the prior two screenshots. After capturing the take a look at information above, a report was generated for the dataset and shared with the wi-fi group for troubleshooting.
Cell Machine Mangement, by Paul Fidler and Connor Loughlin
For the seventh consecutive Black Hat convention, we supplied iOS cell machine administration (MDM) and safety. At Black Hat USA 2023, we have been requested to handle and safe:
- Registration: 32 iPads
- Session Scanning: 51 iPads
- Lead Retrieval: 550 iPhones and 300 iPads

Once we arrived for arrange three days earlier than the beginning of the coaching courses, our mission was to have a community up and working as quickly as is humanly potential, so begin managing the 900+ units and verify their standing.
Wi-Fi Issues
We needed to regulate our Wi-Fi authentication schema. Within the prior 4 Black Hat conferences, the iOS units have been provisioned with a easy PSK primarily based SSID that was out there in all places all through the venue. Then, as they enrolled, they have been additionally pushed a certificates / Wi-Fi coverage (the place the machine then went off and requested a cert from a Meraki Certificates Authority, guaranteeing that the personal key resided securely on the machine. On the similar time, the certificates title was additionally written into Meraki’s Cloud Radius.
Because the machine now had TWO Wi-Fi profiles, it was now free to make use of its inbuilt prioritisation listing (extra particulars right here) guaranteeing that the machine joined the safer of the networks (802.1x primarily based, fairly than WPA2 / PSK primarily based). As soon as we have been certain that each one units have been on-line and checking in to MDM, we then eliminated the cert profile from the units that have been solely used for Lead Retrieval, because the purposes used for this have been web dealing with. Registration units hook up with an software that’s truly on the Black Hat community, therefore the distinction in community necessities.
For Black Hat USA 2023, we simply didn’t have time to formulate a plan for the units that may enable people who wanted to have elevated community authentication capabilities (EAP-TLS in all chance), because the units weren’t connecting to a Meraki community anymore, which might have enabled them to make use of the Sentry functionality, however as a substitute an Arista community.

For the longer term, we are able to do considered one of two issues:
- Provision ALL units with the identical Wi-Fi creds (both Registration or Attendee) Wi-Fi on the time of enrolment and add the related safer creds (cert, possibly) as they enroll to the Registration iPads ONLY
- Extra laboriously, provision Registration units and Session Scanning / Lead Retrieval units with totally different credentials on the time of enrolment. That is much less optimum as:
- We’d have to know forward of time which units are which used for Session Scanning, Lead Retrieval or Registration
- It will introduce the prospect of units being provisioned with the flawed Wi-Fi community creds
When a Wi-Fi profile is launched on the time of Supervision, it stays on the machine always and can’t be eliminated, so possibility 2 actually does have the chance to introduce many extra points.

Automation – Renaming units
Once more, we used the Meraki API and a script that goes off, for a given serial quantity, and renames the machine to match the asset variety of the machine. This has been fairly profitable and, when matched with a coverage displaying the Asset quantity on the Residence Display screen, makes discovering units fast. Nevertheless, the spreadsheets can have information errors in them. In some circumstances, the anticipated serial quantity is the machine title and even an IMEI. While we are able to specify MAC, Serial and SM machine ID as an identifier, we are able to’t (but) provide IMEI.
So, I’ve needed to amend my script in order that it, when it first runs, will get the whole listing of enrolled units and a primary set of inventories, permitting us to lookup issues like IMEI, machine title, and so on., returning a FALSE if nonetheless not discovered or returning the Serial if discovered. This was then amended additional to go looking the Title key if IMEI didn’t return something. It might, theoretically, be expanded to incorporate any of the machine attributes! Nevertheless, I believe we’d run rapidly into false positives.
The identical script was then copied and amended so as to add tags to units. Once more, every machine has a persona:
- Registration
- Lead Retrieval
- Session Scanning
Every persona has a special display screen format and software required. So, to make this versatile, we use tags in Meraki Techniques Supervisor converse. Because of this should you tag a tool, and tag a setting or software, that machine will get that software, and so forth. As Techniques Supervisor helps a complete bunch of tag sorts, this makes it VERY versatile close to complicated standards for who will get what!
Nevertheless, manually tagging units within the Meraki Dashboard would take endlessly, so we are able to utilise an API to do that. I simply needed to change the API name being made for the renaming script, add a brand new column into the CSV with the tag title, and a few different sundry issues. Nevertheless, it didn’t work. The issue was that the renaming API doesn’t care that the ID that’s used: MAC, Serial or SM Machine ID. The Tagging API does, and you need to specify which ID that you just’re utilizing. So, I’d modified the Various Machine ID search technique to return serial as a substitute of SM machine ID. Serial doesn’t exist when doing a tool lookup, however SerialNumber does! A fast edit and several other hundred units had been retagged.
In fact, subsequent time, all of this will likely be performed forward of time fairly than on the convention! Having good information forward of time is priceless, however you may by no means rely on it!
Caching Server
Downloading iOS 16.6 is a hefty 6GB obtain. And while the delta replace is a mere 260MB, that is nonetheless impactful on the community. While the obtain takes a while, this might be massively improved through the use of a caching server. While there’s many alternative ways in which this might be achieved, we’re going to analysis utilizing the caching functionality constructed into macOS (please see documentation right here). The rational for that is that:
- It helps auto uncover, thus there’s no have to construct the content material caching on the fringe of the community. It may be constructed anyplace, and the units will auto uncover this
- It’s astoundingly easy to arrange
- Will probably be caching each OS (Working System) updates AND software updates
While there wasn’t time to get this arrange for Black Hat USA 2023, this will likely be put into manufacturing for future occasions. The one factor we can’t resolve is the humongous period of time the machine must put together a software program replace for set up!
Wi-fi
Predictably (and I solely say that as a result of we had the identical subject final 12 months with Meraki as a substitute of Arista doing the Wi-Fi), the Registration iPads suffered from astoundingly poor obtain speeds and latency, which can lead to the Registration app hanging and attendees not having the ability to print their badges.
We’ve three necessities in Registration:
- Basic Attendee Wi-Fi
- Lead Retrieval and Session Scanning iOS units
- Registration iOS units
The difficulty stems from when each Attendee SSID and Registration SSID are being broadcast from the identical AP. It simply will get hammered, ensuing within the aforementioned points.
The takeaway from that is:
- There must be a devoted SSID for Registration units
- There must be a devoted SSID all through Black Hat for Periods Scanning and Lead Retrieval (This may be the identical SSID, simply dynamic or identification (naming modifications relying on vendor) PSK)
- There must be devoted APs for the iOS units in heavy site visitors areas and
- There must be devoted APs for Attendees in heavy site visitors areas
Lock Display screen Message
Once more, one other studying that got here too late. Due to the vulnerability that was mounted in iOS 16.6 (which got here out the very day that the units have been shipped from Choose2Rent to Black Hat, who ready them), a substantial period of time was spent updating the units. We will add a Lock Display screen message to the units, which present states: ASSET # – SERIAL # Property of Swapcard
Given {that a} go to to a easy webpage was sufficient to make the machine susceptible, it was crucial that we up to date as many as we might.
Nevertheless, while we might see with ease the OS model in Meraki Techniques Supervisor, this wasn’t the case on the machine: You’d must go and open Settings > Basic > About to get the iOS Model.
So, the ideas occurred to me to make use of the Lock Display screen Message to indicate the iOS model as properly! We’d do that with a easy change to the profile. Because the OS Model modifications on the machine, Meraki Techniques Supervisor would see that the profile contents had modified and push the profile once more to the machine! One to implement for the following Black Hat!
The Ugly….
On the night of the day of the Enterprise Corridor, there was a brand new model of the Black Hat / Lead Retrieval app revealed within the Apple App Retailer. Sadly, not like Android, there’s no profiles for Apple that decide the precedence of App updates from the App Retailer. There’s, nevertheless, a command that may be issued to verify for and set up updates.
In three hours, we managed to get practically 25% of units up to date, however, if the consumer is utilizing the app on the time of the request, they’ve the facility to say no the replace.
The Irritating…
For the primary time, we had just a few units go lacking. It’s unsure as as to whether these units are misplaced or stolen, however…
In previous Black Hat occasions, once we’ve had the synergy between System Supervisor and Meraki Wi-Fi, it’s been trivial, as inbuilding GPS (World Positioning System) just isn’t existent, to have a single click on between machine and AP and vice versa. We’ve clearly misplaced that with one other vendor doing Wi-Fi, however, on the very least, we’ve been in a position to feed again the MAC of the machine and get an AP location.
Nevertheless, the opposite irritating factor is that the units are NOT in Apple’s Automated Machine Enrollment. Because of this we lose a few of the safety performance: Activation Lock, the flexibility to power enrollment into administration after a tool wipe, and so on.

All just isn’t misplaced although: As a result of the units are enrolled and supervised, we are able to put them into Misplaced Mode which locks the machine, permits us to place a persistent message on the display screen (even after reboot) and make sure that the cellphone has an audible warning even when muted.
You could find the code and information at this GitHub repository and the information in this weblog publish.
SOC Cubelight, by Ian Redden
The Black Hat NOC Cubelight was impressed by a number of initiatives primarily the 25,000 LED Adafruit Matrix Dice (Overview | RGB LED Matrix Dice with 25,000 LEDs | Adafruit Studying System). Apart from the mounting and orientation of this 5-sided dice, that’s the place the Cubelight differs from different initiatives.
The Raspberry Zero 2W powered gentle makes use of customized written Python to show alerts and statistics from:
- Cisco Umbrella
- NetWitness
- Variety of clear-text passwords noticed and protocol breakdown
- TLS encrypted site visitors vs non-encrypted site visitors
- Cisco ThousandEyes
- BGP Reachability
- Complete Alerts
- DNS Decision in milliseconds
- HTTP Server Availability (%)
- Endpoint Common Throughput (Mbps)
- Endpoint Latency
![]()

Automating the Administration of Umbrella Inside Networks, by Christian Clausen
The Black Hat community is in actual fact a group of over 100 networks, every devoted to logical segments together with the NOC infrastructure, particular person coaching courses, and the general public attendee wi-fi. DNS decision for all these networks is supplied by Umbrella Digital Home equipment: native resolvers deployed onsite. These resolvers helpfully present the inner IP deal with (and subsequently community subnet) for DNS queries. This info is beneficial for enrichment within the SOAR and XDR merchandise utilized by NOC workers. However fairly than having to manually reference a spreadsheet to map the particular community to a question, we are able to mechanically label them within the Umbrella reporting information.
Cisco Umbrella permits for the creation of “Inside Networks” (an inventory of subnets that map to a selected website and label).

With these networks outlined, NOC workers can see the title of the community within the enriched SOAR and XDR information and have extra context when investigating an occasion. However manually creating so many networks could be error inclined and time-consuming. Fortunately, we are able to use the Umbrella API to create them.
The community definitions are maintained by the Black Hat NOC workers in a Google Sheet; and is constantly up to date because the community is constructed, and entry factors deployed. To maintain up with any modifications, we leveraged the Google Sheets API to consistently ballot the community info and reconcile it with the Umbrella Inside Networks. By placing this all collectively in a scheduled job, we are able to hold the community location information correct even because the deployment evolves and networks transfer.
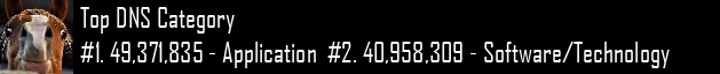
DNS Visibility, Statistics, and Footwear by Alex Calaoagan
One other Black Hat has come and gone, and, if DNS site visitors is any indication, this was by far the largest with near 80 million DNS requests made. As compared, final 12 months we logged simply over 50 million. There are a number of components within the bounce, the first being that we now, because of Palo Alto Networks, seize customers that hardcode DNS on their machines. We did the identical factor in Singapore.
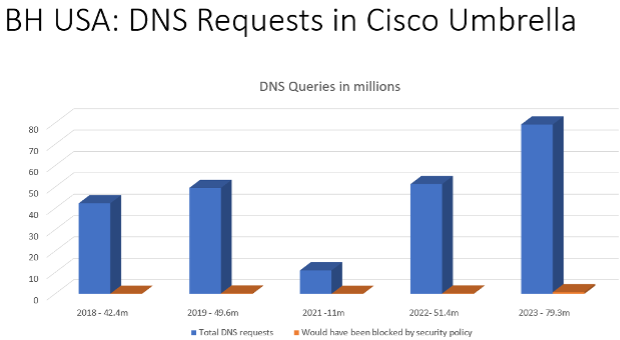
In case you missed it, right here’s the gist: Palo Alto Networks NAT’ed the masked site visitors by way of our Umbrella digital home equipment on website. Site visitors beforehand masked was now seen and trackable by VLAN. This added visibility improved the standard of our statistics, supplying information that was beforehand a black field. Test again in 2024 to see how this new info tracks.

Digging into the numbers, we witnessed simply over 81,000 safety occasions, an enormous drop off from current years. 1.3 million requests have been logged final 12 months, nevertheless that quantity was closely pushed by Dynamic DNS and Newly Seen area occasions. Take away these two excessive quantity classes, and the numbers monitor a lot better.
As all the time, we proceed to see an increase in app utilization at Black Hat:
- 2019: ~3,600
- 2021: ~2,600
- 2022: ~6,300
- 2023: ~7,500

Two years faraway from the pandemic, plainly Black Hat is again on its pure development trajectory, which is superior to see.
Taking a look at Social Media utilization, you may as well see that the group at Black Hat continues to be dominated by Gen X-ers and Millennials with Fb being #1, although the Gen Z crowd is making their presence felt with TikTok at #2. Or is that this a sign of social media managers being savvier? I’m guessing it’s a little bit of each.
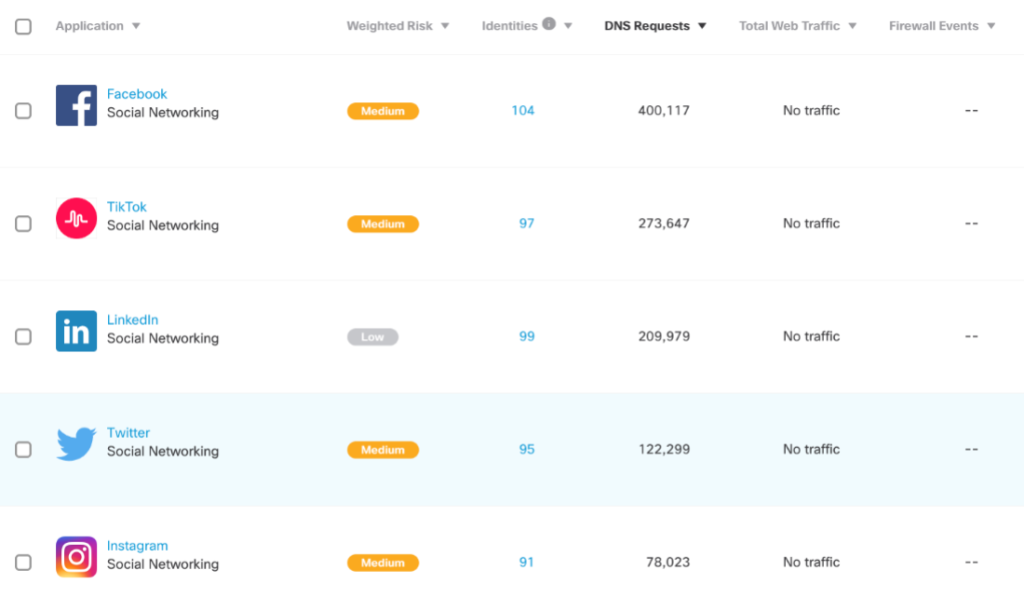
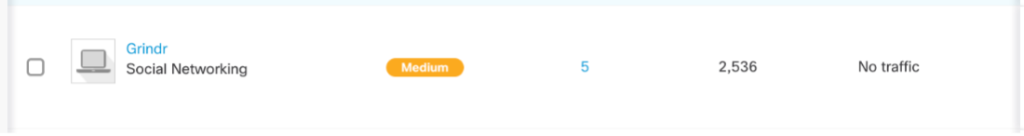
Curious what courting app dominated Black Hat this 12 months? Tinder outpaced Grindr with over double the requests made.


Among the many many developments I noticed on the present ground, one actually caught with me, and it’s one all Distributors hopefully paid shut consideration to.
Of all of the displays and demoes I watched or noticed gathered, one single giveaway drew the biggest and most constant crowds (and most leads).
It’s an merchandise close to and expensive to my coronary heart, and if it’s not close to and expensive to your coronary heart, I’m certain it’s to somebody in your circle. Whether or not it’s in your children, spouse, associate, or shut buddy, while you’re away out of your family members for an prolonged interval, nothing matches higher as an” I missed you” convention reward, until the attendee goes after it for themselves.
What’s it, you ask? Footwear. Nikes to be particular. Jordans, Dunks, and Air Maxes to be much more particular. I counted three cubicles gifting away customized kicks, and each drawing I witnessed (signed up for 2 myself) had crowds flowing into aisles, standing room solely. And sure, like somebody you doubtless know, I’m a Sneakerhead.
Black Hat has all the time had a pleasant subculture twang to it, although it has dulled through the years. You don’t see many excessive mohawks or Viking hats nowadays. Possibly that enjoyable nonetheless exists at Defcon, however Black Hat is now all Company, on a regular basis. Quite a bit has modified since my first Black Hat at Caeser’s Palace in 2011, it truly is a disgrace. That’s why seeing sneaker giveaways makes me smile. They remind me of the subculture that outlined Black Hat again within the day.
The Black Hat present ground itself has change into a Nerd/Sneakerhead showcase. I noticed a pair of Tiffany Dunks and several other totally different iterations of Travis Scott’s collabs. I even noticed a pair of De La Soul Dunks (considered one of my private favorites, and really uncommon). I believe excessive finish kicks have formally change into socially acceptable as enterprise informal, and it warms my coronary heart.
The ethical of this little remark? Distributors, should you’re studying this and have had bother within the lead gathering division, the reply is straightforward. Footwear. We want extra sneakers.
Cheers from Las Vegas ????.
—-
We’re happy with the collaboration of the Cisco group and the NOC companions. Black Hat Europe will likely be in December 2023 on the London eXcel Centre.
Acknowledgments
Thanks to the Cisco NOC group:
- Cisco Safe: Christian Clasen, Alex Calaoagan, Aditya Sankar, Ben Greenbaum, Ryan Maclennan, Ian Redden, Adam Kilgore; with digital help by Steve Nowell
- Meraki Techniques Supervisor: Paul Fidler and Connor Loughlin
- Talos Incident Response: Jerzy ‘Yuri’ Kramarz
Additionally, to our NOC companions: NetWitness (particularly David Glover, Iain Davidson and Alessandro Zatti), Palo Alto Networks (particularly Jason Reverri), Corelight (particularly Dustin Lee), Arista (particularly Jonathan Smith), Lumen and the whole Black Hat / Informa Tech workers (particularly Grifter ‘Neil Wyler,’ Bart Stump, Steve Fink, James Pope, Mike Spicer, Sandy Wenzel, Heather Williams, Jess Stafford and Steve Oldenbourg).

About Black Hat
For 26 years, Black Hat has supplied attendees with the very newest in info safety analysis, improvement, and developments. These high-profile international occasions and trainings are pushed by the wants of the safety group, striving to convey collectively the very best minds within the business. Black Hat conjures up professionals in any respect profession ranges, encouraging development and collaboration amongst academia, world-class researchers, and leaders in the private and non-private sectors. Black Hat Briefings and Trainings are held yearly in the USA, Europe and USA. Extra info is on the market at: Black Hat.com. Black Hat is dropped at you by Informa Tech.
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share:
Related Posts
- Black Hat USA 2023 NOC: Community Assurance
The Black Hat Community Operations Heart (NOC) offers a excessive safety, excessive availability community in…
- 2023 Armlifting USA World Championships to be Held at 2023 Olympia Weekend
Joe Weider was identified for his predictions concerning the evolution of health in addition to…
- Greatest UGG Black Friday Offers to Store in 2023
Though we’re looking out for presents for our family members, we additionally plan to make…